Cybersecurity researchers have uncovered a sophisticated new botnet that is actively exploiting Voice over Internet Protocol (VoIP) enabled routers, primarily by leveraging easily guessable or default factory passwords. The discovery, initially pinpointed to a concentrated cluster of activity in rural New Mexico, has since revealed a global network of compromised devices, highlighting a persistent and often overlooked vulnerability in internet-connected infrastructure.
The alarm was first raised by engineers at GreyNoise Intelligence, who observed an unusual surge of malicious IP addresses originating from a small, sparsely populated region of New Mexico. Further investigation revealed that approximately 90 IP addresses in this area were linked to a single utility authority, exhibiting coordinated botnet behavior through Telnet-based attacks.
Analysis confirmed that 100% of the malicious traffic from this initial cluster was Telnet-based, indicating a systematic targeting of devices with weak authentication protocols. Researchers, utilizing AI-powered analysis and packet capture data, identified many of the affected systems as VoIP-enabled devices, with evidence suggesting the involvement of hardware from manufacturers like Cambium Networks. These compromised systems displayed high-volume Telnet login attempts using weak credentials, aggressive scanning behavior, and characteristics consistent with known Mirai botnet variants.
VoIP devices, often operating on older Linux-based firmware with Telnet services exposed by default, present an attractive target for cybercriminals. They are frequently internet-facing, lightly monitored, and infrequently patched, making them prime candidates for exploitation. Some router models, for instance, may still be running firmware versions vulnerable to remote code execution flaws disclosed years ago.
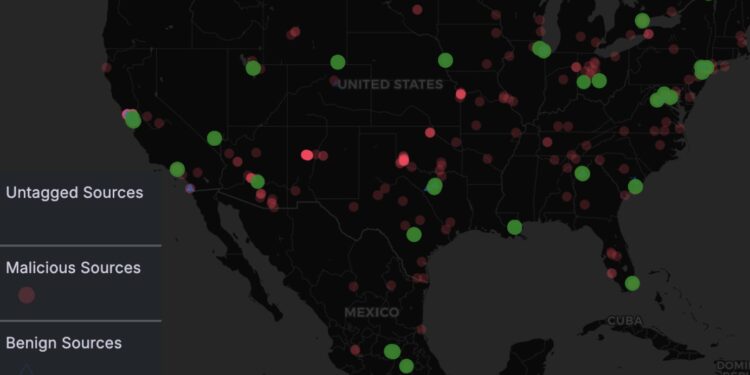
While the activity from the New Mexico utility briefly ceased after a GreyNoise team member mentioned the investigation on social media, the global botnet quickly resumed operations, indicating a tactical shift rather than a shutdown. This incident underscores the critical need for robust security practices across all internet-connected devices.
Security experts are urging organizations and individuals to take immediate action. This includes auditing Telnet exposure on all VoIP-enabled systems, rotating or disabling default credentials on edge devices, and implementing vigilant monitoring for unusual outbound traffic patterns. The proliferation of such botnets highlights how even small utilities and internet service providers can unwittingly become integral parts of global cybercriminal infrastructure if basic security measures, such as changing default passwords and regularly updating firmware, are neglected.