In a troubling new development, threat actors are actively exploiting the very security features designed to protect email users, specifically the link-wrapping services provided by major cybersecurity vendors like Proofpoint and Intermedia. This sophisticated attack vector allows malicious links to bypass traditional email filters and land directly in user inboxes, cloaked in the guise of a trusted and pre-scanned URL.
Link wrapping is a common security measure where an email security gateway rewrites a URL to route it through a vendor’s scanning service at the moment a user clicks. The intention is to inspect the link in real-time and block it if it’s found to be malicious. For example, a link to a suspicious site would be rewritten to something like urldefense.proofpoint.com or url.emailprotection.link.
Attackers have found a way to “launder” their phishing links through these trusted services. The primary method involves compromising an email account that is already protected by one of these services. When the attacker sends a malicious URL from this compromised account, the security gateway automatically wraps the link, effectively giving it a stamp of legitimacy. This wrapped URL, now appearing to originate from a trusted domain, can easily evade other security filters and reputation checks.
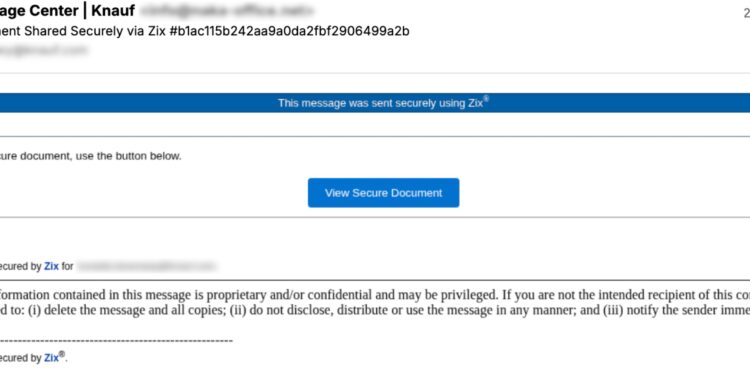
Once clicked, the wrapped URL initiates a series of redirects, often through multiple layers of obfuscation, to a phishing landing page. These pages are meticulously crafted to impersonate popular services like Microsoft 365 or Microsoft Teams, tricking users into entering their credentials. The user, seeing a familiar and seemingly legitimate URL, is less likely to be suspicious, significantly increasing the success rate of the phishing campaign.
Cybersecurity researchers have observed a number of these campaigns, with attackers using compromised accounts to send out emails disguised as voicemail notifications, shared documents, or other urgent requests. In some cases, attackers are adding an extra layer of deception by first using a URL shortening service like Bitly before the link is wrapped, creating a multi-tiered redirection chain that is even harder to detect.
The exploitation of these trusted security mechanisms highlights a significant paradox: when security controls are not sufficiently robust, they can be weaponized by adversaries. As threat actors continue to adapt, security teams must move beyond simple reputation-based filtering and implement more dynamic, behavioral analysis to identify and mitigate these increasingly clever attacks.