Microsoft is being investigated by the FTC over antitrust concerns
Microsoft is being investigated by the Federal Trade Commission in a wide-ranging antitrust probe, making it the fifth Big Tech...
FTC changes its telemarketing rules to cover growing ‘tech support scam’ calls
The Federal Trade Commission (FTC) has finalized amendments to its Telemarketing Sales Rule (TSR), making it easier to protect consumers who are...
Storm-1977 Hits Education Clouds with AzureChecker, Deploys 200+ Crypto Mining Containers
Storm-1977 Hits Education Clouds with AzureChecker, Deploys 200+ Crypto Mining Containers
Are We Ready for the Next Cyber Storm?
Every device, every account, every endpoint is now a potential gateway for intrusion. Are We Ready for the Next Cyber...
ToyMaker Uses LAGTOY to Sell Access to CACTUS Ransomware Gangs for Double Extortion
ToyMaker Uses LAGTOY to Sell Access to CACTUS Ransomware Gangs for Double Extortion
Pete Hegseth’s Signal Scandal Spirals Out of Control
Pete Hegseth’s Signal Scandal Spirals Out of Control
North Korean Hackers Spread Malware via Fake Crypto Firms and Job Interview Lures
North Korean Hackers Spread Malware via Fake Crypto Firms and Job Interview Lures
The Download: how Trump’s tariffs will affect US manufacturing, and AI architecture
The Download: how Trump’s tariffs will affect US manufacturing, and AI architecture
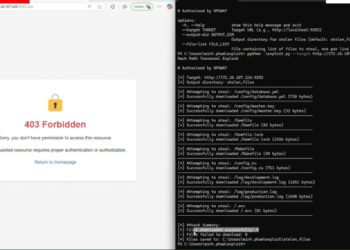
New Critical SAP NetWeaver Flaw Exploited to Drop Web Shell, Brute Ratel Framework
New Critical SAP NetWeaver Flaw Exploited to Drop Web Shell, Brute Ratel Framework
Why NHIs Are Security’s Most Dangerous Blind Spot
Why NHIs Are Security's Most Dangerous Blind Spot
Sweeping tariffs could threaten the US manufacturing rebound
Sweeping tariffs could threaten the US manufacturing rebound
Researchers Identify Rack::Static Vulnerability Enabling Data Breaches in Ruby Servers
Researchers Identify Rack::Static Vulnerability Enabling Data Breaches in Ruby Servers
DslogdRAT Malware Deployed via Ivanti ICS Zero-Day CVE-2025-0282 in Japan Attacks
DslogdRAT Malware Deployed via Ivanti ICS Zero-Day CVE-2025-0282 in Japan Attacks
Protecting Your Phone, and Your Privacy, at the US Border
Protecting Your Phone—and Your Privacy—at the US Border
Gmail’s New Encrypted Messages Feature Opens a Door for Scams
Gmail’s New Encrypted Messages Feature Opens a Door for Scams
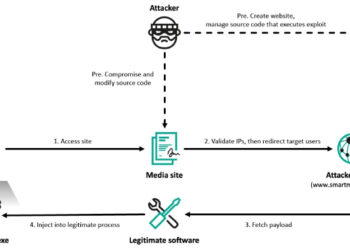
Lazarus Hits 6 South Korean Firms via Cross EX, Innorix Flaws and ThreatNeedle Malware
Lazarus Hits 6 South Korean Firms via Cross EX, Innorix Flaws and ThreatNeedle Malware
Driving business value by optimizing the cloud
Driving business value by optimizing the cloud
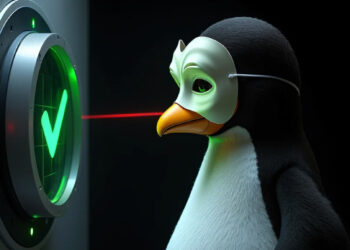
Linux io_uring PoC Rootkit Bypasses System Call-Based Threat Detection Tools
Linux io_uring PoC Rootkit Bypasses System Call-Based Threat Detection Tools