Automating Zero Trust in Healthcare: From Risk Scoring to Dynamic Policy Enforcement Without Network Redesign
Automating Zero Trust in Healthcare: From Risk Scoring to Dynamic Policy Enforcement Without Network Redesign
159 CVEs Exploited in Q1 2025 , 28.3% Within 24 Hours of Disclosure
159 CVEs Exploited in Q1 2025 — 28.3% Within 24 Hours of Disclosure
The Download: Apple’s eucalyptus carbon bet, and climate tech’s bad vibes
The Download: Apple’s eucalyptus carbon bet, and climate tech’s bad vibes
Darcula Adds GenAI to Phishing Toolkit, Lowering the Barrier for Cybercriminals
Darcula Adds GenAI to Phishing Toolkit, Lowering the Barrier for Cybercriminals
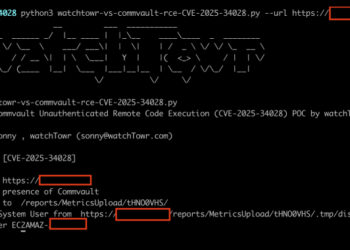
Critical Commvault Command Center Flaw Enables Attackers to Execute Code Remotely
Critical Commvault Command Center Flaw Enables Attackers to Execute Code Remotely
The vibes are shifting for US climate tech
The vibes are shifting for US climate tech
Inside the controversial tree farms powering Apple’s carbon neutral goal
Inside the controversial tree farms powering Apple’s carbon neutral goal
WhatsApp Adds Advanced Chat Privacy to Blocks Chat Exports and Auto-Downloads
WhatsApp Adds Advanced Chat Privacy to Blocks Chat Exports and Auto-Downloads
Roundtables: Brain-Computer Interfaces: From Promise to Product
Roundtables: Brain-Computer Interfaces: From Promise to Product
DPRK Hackers Steal $137M from TRON Users in Single-Day Phishing Attack
DPRK Hackers Steal $137M from TRON Users in Single-Day Phishing Attack
Iran-Linked Hackers Target Israel with MURKYTOUR Malware via Fake Job Campaign
Iran-Linked Hackers Target Israel with MURKYTOUR Malware via Fake Job Campaign
Android Spyware Disguised as Alpine Quest App Targets Russian Military Devices
Android Spyware Disguised as Alpine Quest App Targets Russian Military Devices
The Download: introducing the Creativity issue
The Download: introducing the Creativity issue
Three Reasons Why the Browser is Best for Stopping Phishing Attacks
Three Reasons Why the Browser is Best for Stopping Phishing Attacks
Russian Hackers Exploit Microsoft OAuth to Target Ukraine Allies via Signal and WhatsApp
Russian Hackers Exploit Microsoft OAuth to Target Ukraine Allies via Signal and WhatsApp
3 Things Caiwei Chen is into right now
3 Things Caiwei Chen is into right now
Ripple’s xrpl.js npm Package Backdoored to Steal Private Keys in Major Supply Chain Attack
Ripple's xrpl.js npm Package Backdoored to Steal Private Keys in Major Supply Chain Attack
The Tech That Safeguards the Conclave’s Secrecy
The Tech That Safeguards the Conclave’s Secrecy