Google Drops Cookie Prompt in Chrome, Adds IP Protection to Incognito
Google Drops Cookie Prompt in Chrome, Adds IP Protection to Incognito
Docker Malware Exploits Teneo Web3 Node to Earn Crypto via Fake Heartbeat Signals
Docker Malware Exploits Teneo Web3 Node to Earn Crypto via Fake Heartbeat Signals
GCP Cloud Composer Bug Let Attackers Elevate Access via Malicious PyPI Packages
GCP Cloud Composer Bug Let Attackers Elevate Access via Malicious PyPI Packages
5 Major Concerns With Employees Using The Browser
5 Major Concerns With Employees Using The Browser
Phishers Exploit Google Sites and DKIM Replay to Send Signed Emails, Steal Credentials
Phishers Exploit Google Sites and DKIM Replay to Send Signed Emails, Steal Credentials
Microsoft Secures MSA Signing with Azure Confidential VMs Following Storm-0558 Breach
Microsoft Secures MSA Signing with Azure Confidential VMs Following Storm-0558 Breach
Lotus Panda Hacks SE Asian Governments With Browser Stealers and Sideloaded Malware
Lotus Panda Hacks SE Asian Governments With Browser Stealers and Sideloaded Malware
Kimsuky Exploits BlueKeep RDP Vulnerability to Breach Systems in South Korea and Japan
Kimsuky Exploits BlueKeep RDP Vulnerability to Breach Systems in South Korea and Japan
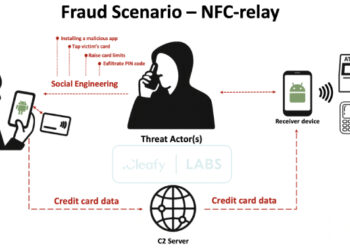
SuperCard X Android Malware Enables Contactless ATM and PoS Fraud via NFC Relay Attacks
SuperCard X Android Malware Enables Contactless ATM and PoS Fraud via NFC Relay Attacks
5 Reasons Device Management Isn’t Device Trust
5 Reasons Device Management Isn't Device Trust
How to Protect Yourself From Phone Searches at the US Border
How to Protect Yourself From Phone Searches at the US Border
⚡ THN Weekly Recap: iOS Zero-Days, 4Chan Breach, NTLM Exploits, WhatsApp Spyware & More
⚡ THN Weekly Recap: iOS Zero-Days, 4Chan Breach, NTLM Exploits, WhatsApp Spyware & More
Hackers Abuse Russian Bulletproof Host Proton66 for Global Attacks and Malware Delivery
Hackers Abuse Russian Bulletproof Host Proton66 for Global Attacks and Malware Delivery
APT29 Deploys GRAPELOADER Malware Targeting European Diplomats Through Wine-Tasting Lures
APT29 Deploys GRAPELOADER Malware Targeting European Diplomats Through Wine-Tasting Lures
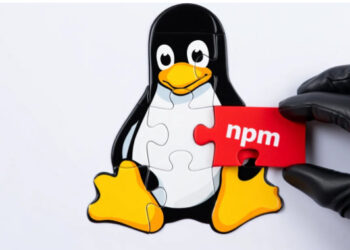
Rogue npm Packages Mimic Telegram Bot API to Plant SSH Backdoors on Linux Systems
Rogue npm Packages Mimic Telegram Bot API to Plant SSH Backdoors on Linux Systems
Florida Man Enters the Encryption Wars
Florida Man Enters the Encryption Wars
ASUS Confirms Critical Flaw in AiCloud Routers; Users Urged to Update Firmware
ASUS Confirms Critical Flaw in AiCloud Routers; Users Urged to Update Firmware
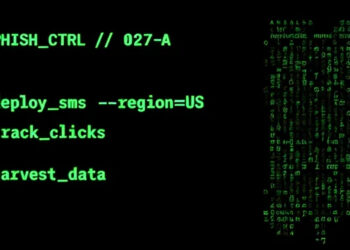
Chinese Smishing Kit Powers Widespread Toll Fraud Campaign Targeting U.S. Users in 8 States
Chinese Smishing Kit Powers Widespread Toll Fraud Campaign Targeting U.S. Users in 8 States