ICE Is Paying Palantir $30 Million to Build ‘ImmigrationOS’ Surveillance Platform
ICE Is Paying Palantir $30 Million to Build ‘ImmigrationOS’ Surveillance Platform
Multi-Stage Malware Attack Uses .JSE and PowerShell to Deploy Agent Tesla and XLoader
Multi-Stage Malware Attack Uses .JSE and PowerShell to Deploy Agent Tesla and XLoader
[Webinar] AI Is Already Inside Your SaaS Stack , Learn How to Prevent the Next Silent Breach
AI Is Already Inside Your SaaS Stack — Learn How to Prevent the Next Silent Breach
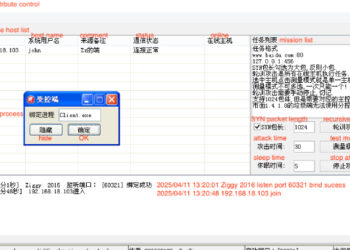
Experts Uncover New XorDDoS Controller, Infrastructure as Malware Expands to Docker, Linux, IoT
Experts Uncover New XorDDoS Controller, Infrastructure as Malware Expands to Docker, Linux, IoT
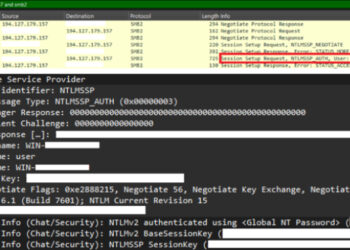
CVE-2025-24054 Under Active Attack, Steals NTLM Credentials on File Download
CVE-2025-24054 Under Active Attack—Steals NTLM Credentials on File Download
Mustang Panda Targets Myanmar With StarProxy, EDR Bypass, and TONESHELL Updates
Mustang Panda Targets Myanmar With StarProxy, EDR Bypass, and TONESHELL Updates
New Jersey Sues Discord for Allegedly Failing to Protect Children
New Jersey Sues Discord for Allegedly Failing to Protect Children
State-Sponsored Hackers Weaponize ClickFix Tactic in Targeted Malware Campaigns
State-Sponsored Hackers Weaponize ClickFix Tactic in Targeted Malware Campaigns
Artificial Intelligence – What’s all the fuss?
Artificial Intelligence – What's all the fuss?
Critical Erlang/OTP SSH Vulnerability (CVSS 10.0) Allows Unauthenticated Code Execution
Critical Erlang/OTP SSH Vulnerability (CVSS 10.0) Allows Unauthenticated Code Execution
Blockchain Offers Security Benefits – But Don’t Neglect Your Passwords
Blockchain Offers Security Benefits – But Don't Neglect Your Passwords
This ‘College Protester’ Isn’t Real. It’s an AI-Powered Undercover Bot for Cops
This ‘College Protester’ Isn’t Real. It’s an AI-Powered Undercover Bot for Cops
Node.js Malware Campaign Targets Crypto Users with Fake Binance and TradingView Installers
Node.js Malware Campaign Targets Crypto Users with Fake Binance and TradingView Installers
CISA Flags Actively Exploited Vulnerability in SonicWall SMA Devices
CISA Flags Actively Exploited Vulnerability in SonicWall SMA Devices
Apple Patches Two Actively Exploited iOS Flaws Used in Sophisticated Targeted Attacks
Apple Patches Two Actively Exploited iOS Flaws Used in Sophisticated Targeted Attacks
‘Stupid and Dangerous’: CISA Funding Chaos Threatens Essential Cybersecurity Program
‘Stupid and Dangerous’: CISA Funding Chaos Threatens Essential Cybersecurity Program
Here’s What Happened to Those SignalGate Messages
Here’s What Happened to Those SignalGate Messages
Suspected 4chan Hack Could Expose Longtime, Anonymous Admins
Suspected 4chan Hack Could Expose Longtime, Anonymous Admins




![[Webinar] AI Is Already Inside Your SaaS Stack , Learn How to Prevent the Next Silent Breach [Webinar] AI Is Already Inside Your SaaS Stack , Learn How to Prevent the Next Silent Breach](https://sumtrix.com/wp-content/uploads/2025/04/ai-cyber-P8ljAr-350x250.jpg)