Microsoft Discloses Exchange Server Flaw Enabling Silent Cloud Access in Hybrid Setups
Microsoft has issued a high-severity security advisory for a flaw in its on-premises Exchange Server that could allow attackers to...
Visa Debuts Program to Help Clients Assess Cyberthreats
In a proactive move to address the escalating threat landscape, Visa has announced the launch of its new Cybersecurity Advisory...
IRGC Hacker Groups Attacking Financial, Government, and Media Organizations
Cybersecurity experts are sounding the alarm as a series of coordinated cyberattacks, attributed to hacker groups with strong ties to...
WhatsApp Takes Down 6.8 Million Accounts Linked to Malicious Activities
In a significant move to combat the rising tide of online fraud, WhatsApp has announced the takedown of over 6.8...
CISA Warns of ‘ToolShell’ Exploits Chain Attacks SharePoint Servers
The Cybersecurity and Infrastructure Security Agency (CISA) has released a dire warning to organizations, urging immediate action against a widespread...
Hackers Use ‘Ghost Calls’ to Abuse Web Conferencing Platforms for Covert C2
Cybersecurity researchers have uncovered a new and highly stealthy technique being used by threat actors, dubbed "ghost calls," to establish...
Foreign adversaries are trying to weaponize open-source software, report finds
A new report reveals that state-sponsored actors are actively and methodically attempting to weaponize open-source software (OSS), posing a significant...
D4rk4rmy Claims Hack of Monte Carlo Resort
The luxurious Monte Carlo Société des Bains de Mer (SBM) group, which operates some of Monaco's most prestigious hotels and...
CrowdStrike Delivers a New Era of Operational Threat Intelligence, Personalized to Each Customer Environment
At the Black Hat USA 2025 conference, cybersecurity leader CrowdStrike announced a significant leap forward in threat intelligence, introducing a...
Palo Alto Networks to Acquire CyberArk for $25B in Major Security Deal
In a blockbuster move that is poised to reshape the cybersecurity landscape, Palo Alto Networks has announced a definitive agreement...
Chanel Hit by Salesforce Data Theft Attacks
Luxury fashion house Chanel is the latest high-profile company to fall victim to a widespread data theft campaign targeting users...
Fake TikTok Domains Spread Malware, Steal Crypto via AI-Driven Scam Campaign
In a new and alarming wave of cybercrime, a sophisticated scam campaign is leveraging AI-driven techniques and a network of...
Android’s August 2025 Update Patches Exploited Qualcomm Vulnerability
Google's August 2025 Android security update is now rolling out, bringing with it critical fixes, including a patch for a...
APT37 Hackers Use JPEGs to Hack Windows
A North Korean state-sponsored hacking group, known as APT37, is deploying a sophisticated and stealthy new tactic to infect Windows...
ATM network breached and attacked through 4G Raspberry Pi
A sophisticated and alarming cyber-physical attack has been uncovered, where a financially motivated threat group successfully breached a bank's ATM...
Everest Ransomware Claims Mailchimp as New Victim in Relatively Small Breach
In a developing story, the infamous Everest ransomware group has added a new name to its list of victims: email...
WhatsApp 0-Click RCE Exploit Worth $1 Million at Pwn2Own Ireland 2025
The cybersecurity world is abuzz following an unprecedented announcement from Trend Micro’s Zero Day Initiative (ZDI) for the upcoming Pwn2Own...
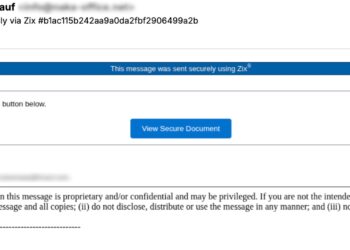
Threat Actors Exploit Proofpoint and Intermedia Link Wrapping to Conceal Phishing Payloads
In a troubling new development, threat actors are actively exploiting the very security features designed to protect email users, specifically...