In one of the most important crackdowns yet on ransomware, law enforcement in multiple countries this week teamed up to take out infrastructure the criminal gangs used to spread such attacks around the world.
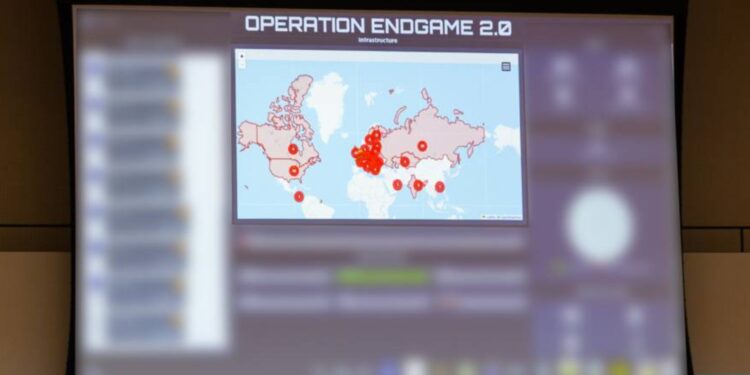
Alongside Europol and Eurojust, we developed an operation between May 19th-22nd 2025 and took down just below 300 servers and 650 malicious domains across the globe.
This current phase of Operation Endgame builds on the previous action in May 2024 in botnets. Endgame 2.0 aimed to obstruct the “initial access” phase of ransomware campaigns, which is carried out to deploy the malware that will get inside a victim’s PC without being detected.
These malware goodies, frequently available as part of a ‘cybercrime-as-a-service’ scam, serve to prime the stage for ransomware.
Operations like this one have already taken down some of the other malware familiar to us such as Bumblebee, Lactrodectus, Qakbot, Hijackloader, Danabot, and Trickbot, and Warmcookie.
When law enforcement disrupts the infrastructure behind them, it seeks to stymie cybercriminal groups’ ability to break into networks and install ransomware.
In addition, 20 prime suspects thought to be orchestrating and facilitating the operation and supply of these initial access services have had international arrest warrants issued for them. In order to bring these people to account, German authorities stated that the names of 18 of these suspects would be added to the EU’s Most Wanted list and that they are asking for the public to help track them down.
Law enforcement authorities from the Canada, Denmark, France, Germany, the Netherlands, the United Kingdom and the United States also participated in the operation, with Europol providing coordination and analytical support, as well as facilitating the real-time exchange of information between the countries. A command post co-ordinated countries from Europol’s headquarters in The Hague.
Aside from removing infrastructure and arrest warrants, Operation Endgame 2.0 also paralyzed a further €3.5 million in cryptocurrency ― this brought the total cryptocurrency paralyzed within the Endgame operations to over €21.2 million.` The financial strike is meant to derail the financial incentives behind ransomware attacks.
Ms Catherine De Bolle, Executive Director of Europol, commented on the vital importance of this operation: “This new phase illustrates the adaptability of law enforcement when it comes to safeguarding the area of cybercrime, even when cybercriminals adopt new ways of doing their business. We are breaking the kill chain at the source by cutting off the services and servers that criminals use to exercise ransomware.”
Admitting that ransomware is a long-standing problem, officials think that Operation Endgame 2.0 has delivered a heavy blow to the underground cybercrime economy. The emphasis on initial access brokers represents a shift in strategy to disrupt attacks before they even start.
Operation Endgame is continuing, and more activity is expected under what Europol says will be a group approach to combating ransomware. The forthcoming 2025 Internet Organised Crime Threat Assessment, by Europol, is anticipated to also emphasize the significant presence of initial access brokers in the ransomware space.